Looking for an Alternative to Akamai App & API Protector?
Secure your APIs and apps with observability, prevention, and protection – within one easy-to-use platform.
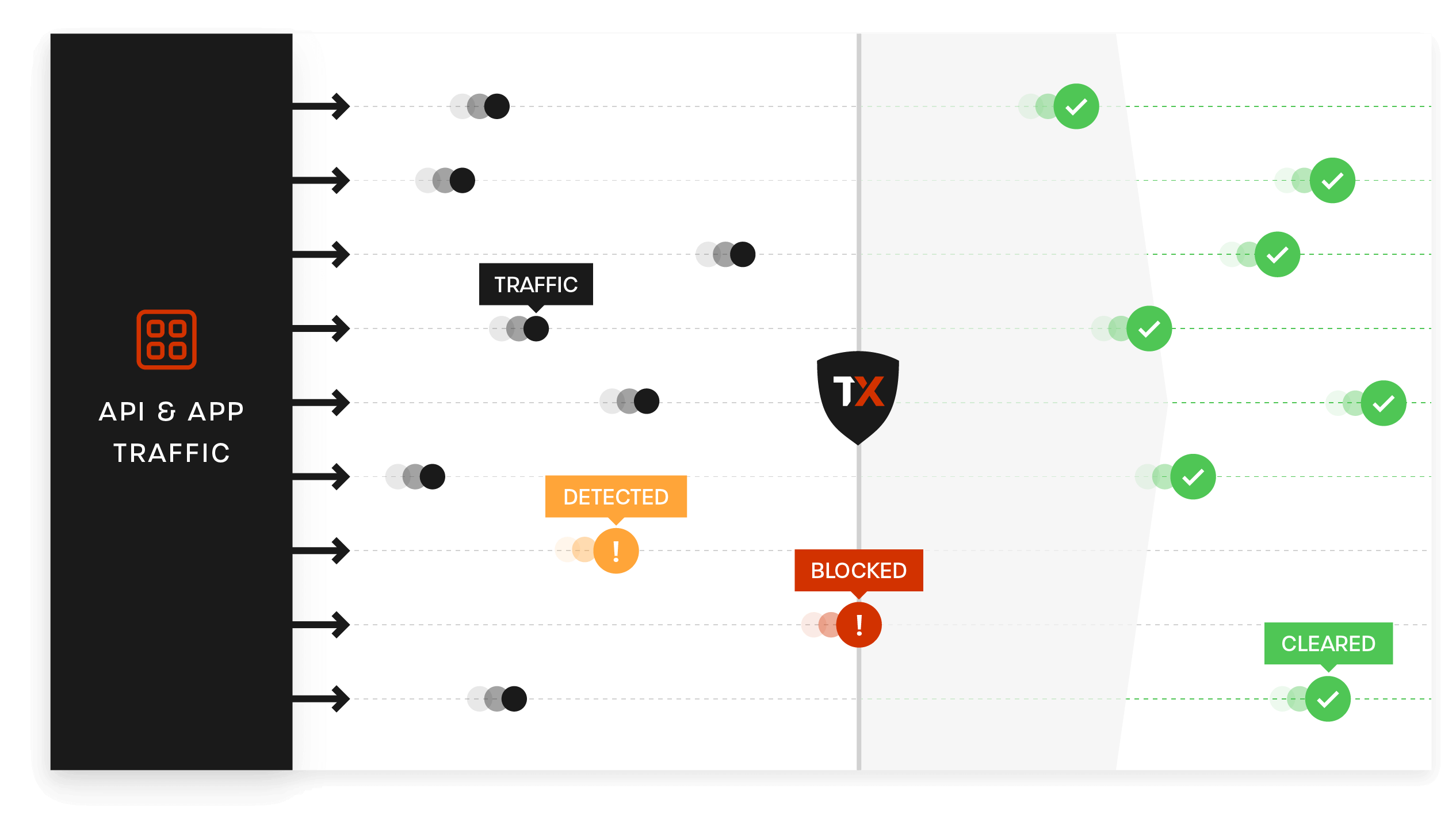
- Identify and stop attacks with automated, risk-based blocking
- Get continuous API discovery, traffic analytics, and threat investigation
- On-board and enable protection for multi-cloud environments in minutes
- Rest easy with fully managed API & app protection, 24/7 support, and more – backed by experts
- Protect APIs and apps against botnets, runtime threats, and other sophisticated attacks within one platform
Why ThreatX Might Be a Fit for Your Organization
Prospects often come to us frustrated with how disjointed their WAF, API, and bot protection solutions are in large platforms like Akamai. Getting a clear picture of all of the threats at the edge and at runtime requires multiple product licenses and more infrastructure to manage. ThreatX offers a simpler and more practical approach.
ThreatX customers often value best-of-breed protection, simple management and deployment, along with the partnership they form with our Protection-as-a-Service team as an extension of theirs. Our platform is cloud-native and easily protects APIs and apps across any mix of cloud infrastructure.
| Compare our Solution Features | ThreatX | Akamai |
| Behavioral Threat Detection | ||
| Risk-based Blocking | ||
| Web Application Firewall | ||
| API Protection | ||
| DDoS Protection | ||
| Bot Defense | ||
| Protection-as-a-Service | ||
| API Specification Generation | ||
| API OWASP Top 10 |
Why Prospects Choose ThreatX Over Akamai
Detect and Block Advanced Threats, Automatically
Stay ahead of cyber threats by tracking behavior and blocking based on risk
Detect, track, and block attackers, all with a single solution.
Attackers are always switching up their methods and tactics. With solutions that are signature-based or that rely on static rulesets, this quickly devolves into a never-ending game of cat and mouse. Your team ends up wasting valuable cycles on menial tasks that aren’t making you safer.
ThreatX is always monitoring, assessing, and correlating attacker behavior to quickly and accurately identify threats. Continuously tracking attackers over time, ThreatX provides a complete view of the evolving threats targeting your APIs and applications and blocks them automatically based on risk, reducing false positives and alert fatigue.
Learn more about risk-based blocking with ThreatX.

Key Benefits
Secure APIs and applications with Observability, Prevention, and Protection
Eliminate risks without compromising your time or peace of mind.

Easy-to-Use
Experience user-friendly security designed to focus on what matters most. Leverage simplified dashboards so you can effortlessly oversee your API and application’s security posture and risks.
Easy-to-Manage
Get your nights and weekends back with always-active security that ensures your APIs and applications stay safe. Our visionary technology provides continuous protection and prevention without the need for manual intervention. Enjoy peace of mind knowing that your APIs and applications are secure even when you’re off the clock.
Eliminate Risks
ThreatX solutions are always monitoring, assessing, and identifying risks to APIs and applications continuously based on behavior. Our technology learns to recognize threats and vulnerabilities specific to your system, and proactively stops them based on risk level. This ensures your business remains operational and efficient, without interruptions.
Protect Your APIs and Applications with Confidence, Not Complexity
ThreatX is managed API and application protection that lets you secure them with confidence, not complexity. It blocks botnets and advanced attacks in real time, letting enterprises keep attackers at bay without lifting a finger. Trusted by leaders like Lenovo, BMC and Epsilon, ThreatX profiles attackers and blocks advanced risks to protect APIs and web apps 24/7.